Server 2012 End of Life: What You Need to Know
Kerkhoff Technologies If you are still running Windows Server 2012 or 2012 R2, what will happen when Microsoft ends its support for these operating systems on October 10, 2023? This
Kerkhoff Technologies If you are still running Windows Server 2012 or 2012 R2, what will happen when Microsoft ends its support for these operating systems on October 10, 2023? This

Kerkhoff Technologies In today’s digital landscape, cybersecurity threats continue to evolve. They pose significant risks to individuals and organizations alike. One such threat gaining prominence is zero-click malware. This insidious
Kerkhoff Technologies Remote work has become increasingly popular in recent times. It provides flexibility and convenience for employees. Additionally, telecommuting reduces office costs for employers. Many also cite productivity benefits

Kerkhoff Technologies In today’s digital workplace, printing remains an essential function. This is true for just about all businesses. But keeping up with your print infrastructure can be a time-consuming

Kerkhoff Technologies Moving can be a chaotic and stressful time. Especially when it comes to handling your valuable technology. Whether you’re relocating your home or office, it’s essential to take

We explain how Microsoft Edge is introducing some new security-boosting features to help you stay one step ahead.

Microsoft Teams Meeting Recap will summarize your meetings and even make a list of the action points. We show you its other benefits
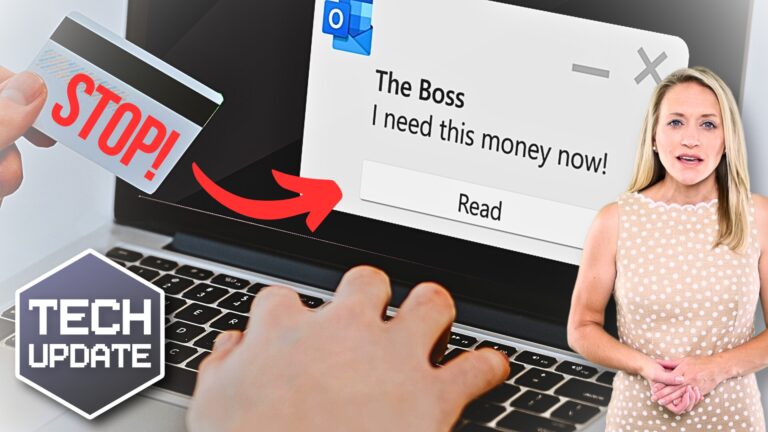
Don’t fall victim to cyber criminals. We explain what a BEC attack is and how to protect your business.

Kerkhoff Technologies Advanced AI is a new buzzword in cloud computing. The launch of tools like ChatGPT and Bard have made big waves. Developers are now racing to introduce the

Kerkhoff Technologies Online shopping has become a common activity for many people. It’s convenient, easy, and allows us to buy items from the comfort of our homes. But with the

Kerkhoff Technologies As cyber threats continue to increase, businesses must take proactive steps. They need to protect their sensitive data and assets from cybercriminals. Threats to data security are persistent

Old computers and external drives can put your sensitive business data at risk.
We tell you how to dispose of them in the safest way possible.
Is your business reliant on technology? Don’t wait for a technical issue to occur before finding a great IT support partner.
Download our free guide to choose the right one for you.

